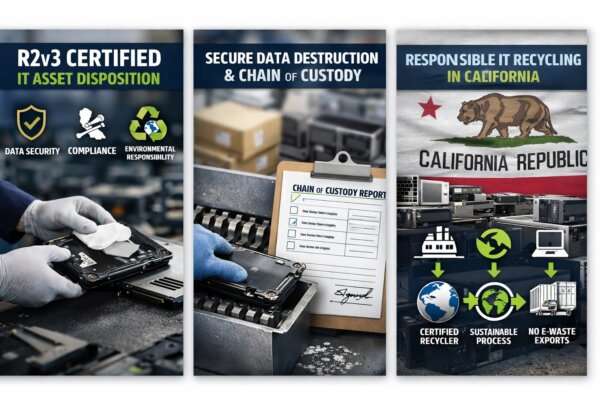
What R2v3 Certification Means for Secure IT Asset Disposition in California
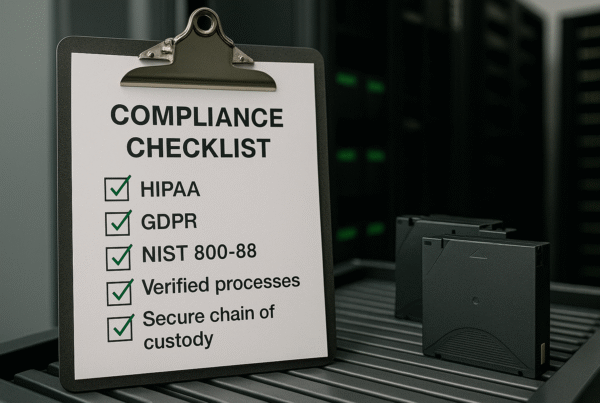
California doesn’t do “average” when it comes to data privacy, environmental oversight, or consumer protection—and that’s exactly why IT Asset Disposition (ITAD) here needs to be held to a higher bar. If you’re a business, school district, healthcare provider, municipality, or any organization managing end-of-life laptops, servers, storage devices, phones, networking gear, or lab equipment, you’re balancing three big risks…